Always On Vpn Cisco Anyconnect
Introduction
- Cisco Anyconnect Vpn Server
- Cisco Anyconnect Client Download
- Cisco Anyconnect Always On Vpn Android
- Cisco Anyconnect Client Vpn
- Cached
- The Anyconnect VPN client has a feature named 'Always On': Always-On operation prevents access to Internet resources when the computer is not on a trusted network, unless a VPN session is active. Enforcing the VPN to always be on in this situation protects the computer from security threats.
- The Cisco VPN supports this and actually allows account level restrictions. Additionally the clientside routes are not defined by Cisco, they're defined by the network admin deploying the production. The VPN client also comes with a separate Firewall solution that is required to be running while the VPN client is running, but can be disabled.
This document describes the Cisco AnyConnect Mobility Client captive portal detection feature and the requirements for it to function correctly. Many wireless hotspots at hotels, restaurants, airports, and other public places use captive portals in order to block user access to the Internet. They redirect HTTP requests to their own websites that require users to enter their credentials or acknowledge terms and conditions of the hotspot host.
If the Always-on VPN is enabled, the connect failure policy is closed, captive portal remediation is disabled, and AnyConnect detects the presence of a captive portal, then the AnyConnect GUI displays this message once per connection and once per reconnect: The service provider in your current location is restricting access to the Internet. Automatically Start VPN Connections When AnyConnect Starts This feature called Auto Connect On Start, automatically establishes a VPN connection with the secure gateway specified by the VPN client profile when AnyConnect starts. Auto Connect On Start is disabled by default, requiring the user to specify or select a secure gateway. In order to access the enterprise intranet remotely, we have to use the Cisco AnyConnect VPN client. We're allowed to install it on any personal machines, and they provide downloads and instructions for Windows, Mac and Linux. This works fine except for the routing table configurations they provide.
Prerequisites
Requirements
Cisco recommends that you have knowledge of the Cisco AnyConnect Secure Mobility Client.
Components Used
The information in this document is based on these software versions:
- AnyConnect Version 3.1.04072
- Cisco Adaptive Security Appliance (ASA) Version 9.1.2
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Background Information
Many facilities that offer Wi-Fi and wired access, such as airports, coffee shops, and hotels, require users to pay before they obtain access, agree to abide by an acceptable use policy, or both. These facilities use a technique called captive portal in order to prevent applications from connecting until users open a browser and accept the conditions for access.
Captive Portal Remediation Requirements
Support for both captive portal detection and remediation requires one of these licenses:
- AnyConnect Premium (Secure Sockets Layer (SSL) VPN Edition)
- Cisco AnyConnect Secure Mobility
You can use a Cisco AnyConnect Secure Mobility license in order to provide support for captive portal detection and remediation in combination with either an AnyConnect Essentials or an AnyConnect Premium license.
Note: Captive portal detection and remediation is supported on the Microsoft Windows and Macintosh OS X operating systems supported by the release of AnyConnect that is in use.
Captive Portal Hotspot Detection
AnyConnect displays the Unable to contact VPN server message on the GUI if it cannot connect, regardless of the cause. The VPN server specifies the secure gateway. If Always-on is enabled and a captive portal is not present, the client continues to attempt to connect to the VPN and updates the status message accordingly.
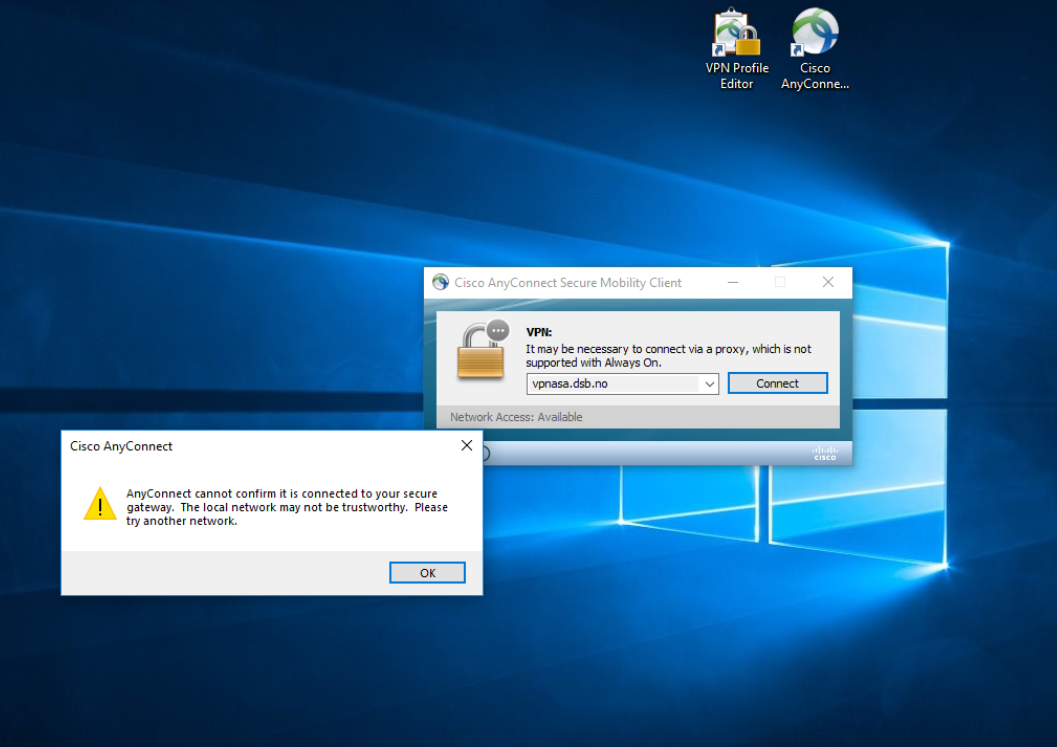
If the Always-on VPN is enabled, the connect failure policy is closed, captive portal remediation is disabled, and AnyConnect detects the presence of a captive portal, then the AnyConnect GUI displays this message once per connection and once per reconnect:
If AnyConnect detects the presence of a captive portal and the AnyConnect configuration differs from that previously described, the AnyConnect GUI displays this message once per connection and once per reconnect:
Caution: Captive portal detection is enabled by default and is nonconfigurable. AnyConnect does not modify any browser configuration settings during captive portal detection.
Captive Portal Hotspot Remediation
Captive portal remediation is the process where you satisfy the requirements of a captive portal hotspot in order to obtain network access.
AnyConnect does not remediate the captive portal; it relies on the end user to perform the remediation.
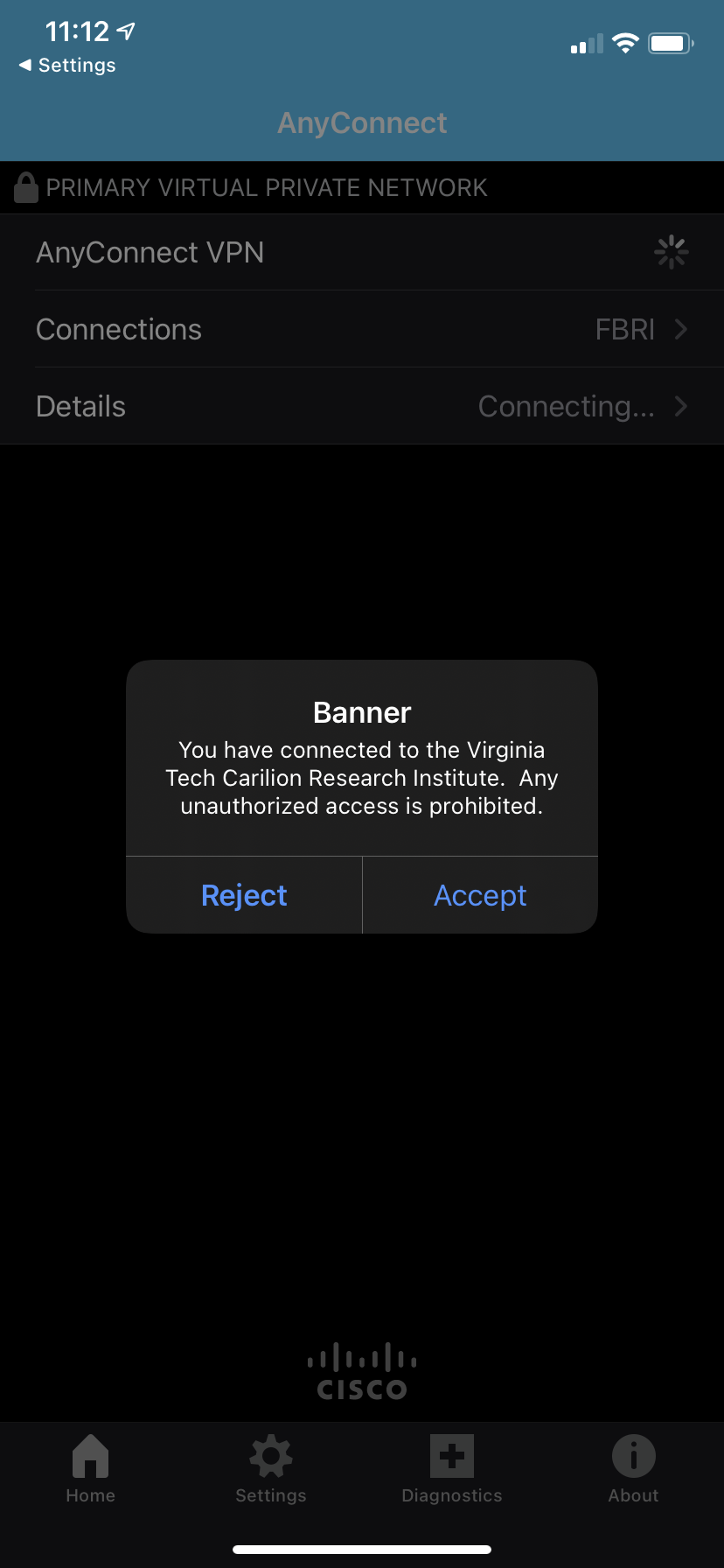
In order to perform the captive portal remediation, the end user meets the requirements of the hotspot provider. These requirements might include payment of a fee to access the network, a signature on an acceptable use policy, both, or some other requirement that is defined by the provider.
Captive portal remediation must be explicitly allowed in an AnyConnect VPN Client profile if AnyConnect Always-on is enabled and the Connect failure policy is set to Closed. If Always-on is enabled and the Connect Failure policy is set to Open, you do not need to explicitly allow captive portal remediation in an AnyConnect VPN Client profile because the user is not restricted from network access.
False Captive Portal Detection
AnyConnect can falsely assume it is in a captive portal in these situations.
- If AnyConnect attempts to contact an ASA with a certificate that contains an incorrect server name (CN), then the AnyConnect client will think it is in a captive portal environment.
In order to prevent this issue, make sure that the ASA certificate is properly configured. The CN value in the certificate must match the name of the ASA server in the VPN client profile. - If there is another device on the network before the ASA that responds to the client's attempt to contact an ASA by blocking HTTPS access to the ASA, then the AnyConnect client will think it is in a captive portal environment. This situation can occur when a user is on an internal network and connects through a firewall in order to connect to the ASA.
If you must restrict access to the ASA from inside the corporation, configure your firewall such that HTTP and HTTPS traffic to the ASA's address does not return an HTTP status. HTTP/HTTPS access to the ASA should either be allowed or completely blocked (also known as black-holed) in order to ensure that HTTP/HTTPS requests sent to the ASA will not return an unexpected response.
AnyConnect Behavior
This section describes how the AnyConnect behaves.
- AnyConnect tries an HTTPS probe to the Fully Qualified Domain Name (FQDN) defined in the XML profile.
- If there is a certificate error (not trusted/wrong FQDN), then AnyConnect tries an HTTP probe to the FQDN defined in the XML profile. If there is any other response than an HTTP 302, then it considers itself to be behind a captive portal.
Captive Portal Incorrectly Detected with IKEV2
When you attempt an Internet Key Exchange Version 2 (IKEv2) connection to an ASA with SSL authentication disabled that runs the Adaptive Security Device Manager (ASDM) portal on port 443, the HTTPS probe performed for captive portal detection results in a redirect to the ASDM portal (/admin/public/index.html). Since this is not expected by the client, it looks like a captive portal redirect, and the connection attempt is prevented since it seems that captive portal remediation is required.
Workarounds
If you encounter this issue, here are some workarounds:
- Remove HTTP commands on that interface so that the ASA will not listen to HTTP connections on the interface.
- Remove the SSL trustpoint on the interface.
- Enable IKEV2 client-services.
- Enable WebVPN on the interface.
This issue is resolved by Cisco bug ID CSCud17825 in Version 3.1(3103).
Caution: The same problem exists for Cisco IOS® routers. If ip http server is enabled on Cisco IOS, which is required if the same box is used as the PKI Server, AnyConnect falsely detects captive portal. The workaround is to use ip http access-class in order to stop responses to AnyConnect HTTP requests, instead of requesting authentication.
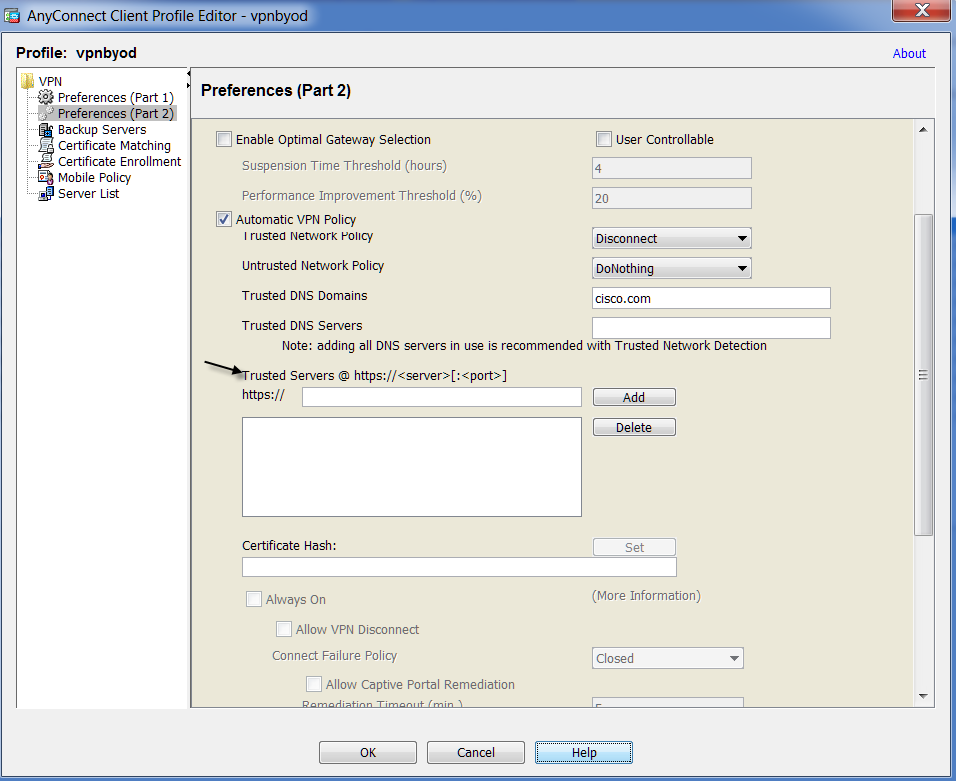
Disable the Captive Portal Feature
It is possible to disable the captive portal feature in AnyConnect client version 4.2.00096 and later (see Cisco bug ID CSCud97386). The administrator can determine if the option should be user configurable or disabled. This option is available under the Preferences (Part 1) section in the profile editor. The administrator can choose Disable Captive Portal Detection or User Controllable as shown in this profile editor snapshot:
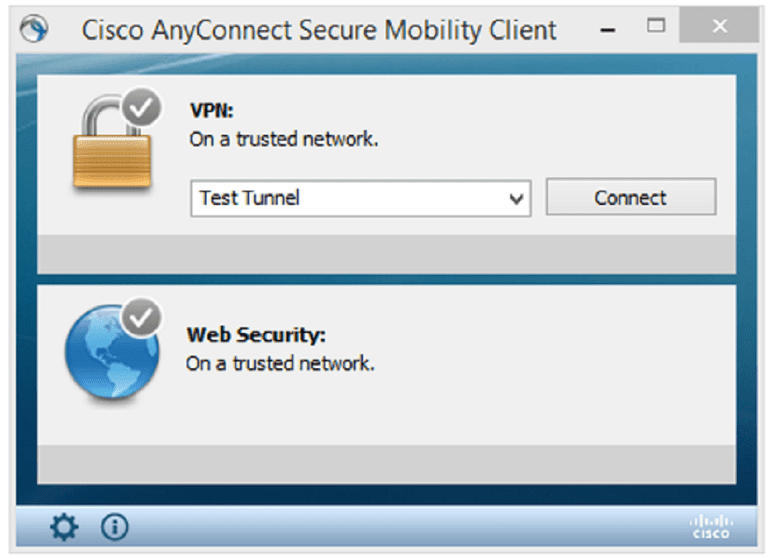
If User controllable is checked, the checkbox appears on the Preferences tab of the AnyConnect Secure Mobility Client UI as shown here:
-->Applies to: Windows Server (Semi-Annual Channel), Windows Server 2016, Windows Server 2012 R2, Windows 10
- Previous: Step 5. Configure DNS and Firewall Settings
In this step, you'll learn about the ProfileXML options and schema, and configure the Windows 10 client computers to communicate with that infrastructure with a VPN connection.
You can configure the Always On VPN client through PowerShell, Microsoft Endpoint Configuration Manager, or Intune. All three require an XML VPN profile to configure the appropriate VPN settings. Automating PowerShell enrollment for organizations without Configuration Manager or Intune is possible.
Note
Group Policy does not include administrative templates to configure the Windows 10 Remote Access Always On VPN client. However, you can use logon scripts.
ProfileXML overview
ProfileXML is a URI node within the VPNv2 CSP. Rather than configuring each VPNv2 CSP node individually—such as triggers, route lists, and authentication protocols—use this node to configure a Windows 10 VPN client by delivering all the settings as a single XML block to a single CSP node. The ProfileXML schema matches the schema of the VPNv2 CSP nodes almost identically, but some terms are slightly different.
You use ProfileXML in all the delivery methods this deployment describes, including Windows PowerShell, Microsoft Endpoint Configuration Manager, and Intune. There are two ways to configure the ProfileXML VPNv2 CSP node in this deployment:
OMA-DM. One way is to use an MDM provider using OMA-DM, as discussed earlier in the section VPNv2 CSP nodes. Using this method, you can easily insert the VPN profile configuration XML markup into the ProfileXML CSP node when using Intune.
Windows Management Instrumentation (WMI)-to-CSP bridge. The second method of configuring the ProfileXML CSP node is to use the WMI-to-CSP bridge—a WMI class called MDM_VPNv2_01—that can access the VPNv2 CSP and the ProfileXML node. When you create a new instance of that WMI class, WMI uses the CSP to create the VPN profile when using Windows PowerShell and Configuration Manager.
Even though these configuration methods differ, both require a properly formatted XML VPN profile. To use the ProfileXML VPNv2 CSP setting, you construct XML by using the ProfileXML schema to configure the tags necessary for the simple deployment scenario. For more information, see ProfileXML XSD.
Below you find each of the required settings and its corresponding ProfileXML tag. You configure each setting in a specific tag within the ProfileXML schema, and not all of them are found under the native profile. For additional tag placement, see the ProfileXML schema.
Important
Any other combination of upper or lower case for 'true' in the following tags results in a partial configuration of the VPN profile:
<AlwaysOn>true</AlwaysOn>
<RememberCredentials>true</RememberCredentials>
Connection type: Native IKEv2
ProfileXML element:
Routing: Split tunneling
ProfileXML element:
Name resolution: Domain Name Information List and DNS suffix
ProfileXML elements:
Triggering: Always On and Trusted Network Detection
ProfileXML elements:
Authentication: PEAP-TLS with TPM-protected user certificates
ProfileXML elements:
You can use simple tags to configure some VPN authentication mechanisms. However, EAP and PEAP are more involved. The easiest way to create the XML markup is to configure a VPN client with its EAP settings, and then export that configuration to XML.
For more information about EAP settings, see EAP configuration.
Manually create a template connection profile
In this step, you use Protected Extensible Authentication Protocol (PEAP) to secure communication between the client and the server. Unlike a simple user name and password, this connection requires a unique EAPConfiguration section in the VPN profile to work.
Instead of describing how to create the XML markup from scratch, you use Settings in Windows to create a template VPN profile. After creating the template VPN profile, you use Windows PowerShell to consume the EAPConfiguration portion from that template to create the final ProfileXML that you deploy later in the deployment.
Record NPS certificate settings
Before creating the template, take note the hostname or fully qualified domain name (FQDN) of the NPS server from the server's certificate and the name of the CA that issued the certificate.
Procedure:
On your NPS server, open Network Policy Server.
In the NPS console, under Policies, click Network Policies.
Right-click Virtual Private Network (VPN) Connections, and click Properties.
Click the Constraints tab, and click Authentication Methods.
In EAP Types, click Microsoft: Protected EAP (PEAP), and click Edit.
Record the values for Certificate issued to and Issuer.
You use these values in the upcoming VPN template configuration. For example, if the server's FQDN is nps01.corp.contoso.com and the hostname is NPS01, the certificate name is based upon the FQDN or DNS name of the server—for example, nps01.corp.contoso.com.
Cancel the Edit Protected EAP Properties dialog box.
Cancel the Virtual Private Network (VPN) Connections Properties dialog box.
Close Network Policy Server.
Note
If you have multiple NPS servers, complete these steps on each one so that the VPN profile can verify each of them should they be used.
Configure the template VPN profile on a domain-joined client computer
Now that you have the necessary information configure the template VPN profile on a domain-joined client computer. The type of user account you use (that is, standard user or administrator) for this part of the process does not matter.
However, if you haven't restarted the computer since configuring certificate autoenrollment, do so before configuring the template VPN connection to ensure you have a usable certificate enrolled on it.
Note
There is no way to manually add any advanced properties of VPN, such as NRPT rules, Always On, Trusted network detection, etc. In the next step, you create a test VPN connection to verify the configuration of the VPN server and that you can establish a VPN connection to the server.
Manually create a single test VPN connection
Sign in to a domain-joined client computer as a member of the VPN Users group. Mac lip crayon.
On the Start menu, type VPN, and press Enter.
In the details pane, click Add a VPN connection.
In the VPN Provider list, click Windows (built-in).
In Connection Name, type Template.
In Server name or address, type the external FQDN of your VPN server (for example, vpn.contoso.com).
Click Save.
Under Related Settings, click Change adapter options.
Right-click Template, and click Properties.
On the Security tab, in Type of VPN, click IKEv2.
In Data encryption, click Maximum strength encryption.
Click Use Extensible Authentication Protocol (EAP); then, in Use Extensible Authentication Protocol (EAP), click Microsoft: Protected EAP (PEAP) (encryption enabled).
Click Properties to open the Protected EAP Properties dialog box, and complete the following steps:
a. In the Connect to these servers box, type the name of the NPS server that you retrieved from the NPS server authentication settings earlier in this section (for example, NPS01).
Note
The server name you type must match the name in the certificate. You recovered this name earlier in this section. If the name does not match, the connection will fail, stating that 'The connection was prevented because of a policy configured on your RAS/VPN server.'
b. Under Trusted Root Certification Authorities, select the root CA that issued the NPS server's certificate (for example, contoso-CA).
c. In Notifications before connecting, click Don't ask user to authorize new servers or trusted CAs.
d. In Select Authentication Method, click Smart Card or other certificate, and click Configure. The Smart Card or other Certificate Properties dialog opens.
e. Click Use a certificate on this computer.
f. In the Connect to these servers box, enter the name of the NPS server you retrieved from the NPS server authentication settings in the previous steps.
g. Under Trusted Root Certification Authorities, select the root CA that issued the NPS server's certificate.
h. Select the Don't prompt user to authorize new servers or trusted certification authorities check box.
i. Click OK to close the Smart Card or other Certificate Properties dialog box.
j. Click OK to close the Protected EAP Properties dialog box.
Click OK to close the Template Properties dialog box.
Close the Network Connections window.
In Settings, test the VPN by clicking Template, and clicking Connect.
Important
Make sure that the template VPN connection to your VPN server is successful. Doing so ensures that the EAP settings are correct before you use them in the next example. You must connect at least once before continuing; otherwise, the profile will not contain all the information necessary to connect to the VPN.
Create the ProfileXML configuration files
Before completing this section, make sure you have created and tested the template VPN connection that the section Manually create a template connection profile describes. Testing the VPN connection is necessary to ensure that the profile contains all the information required to connect to the VPN.
The Windows PowerShell script in Listing 1 creates two files on the desktop, both of which contain EAPConfiguration tags based on the template connection profile you created previously:
VPN_Profile.xml. This file contains the XML markup required to configure the ProfileXML node in the VPNv2 CSP. Use this file with OMA-DM–compatible MDM services, such as Intune.
VPN_Profile.ps1. This file is a Windows PowerShell script that you can run on client computers to configure the ProfileXML node in the VPNv2 CSP. You can also configure the CSP by deploying this script through Configuration Manager. You cannot run this script in a Remote Desktop session, including a Hyper-V enhanced session.
Important
The example commands below require Windows 10 Build 1607 or later.
Create VPN_Profile.xml and VPN_Proflie.ps1
Sign in to the domain-joined client computer containing the template VPN profile with the same user account that the section Manually create a template connection profile described.
Paste Listing 1 into Windows PowerShell integrated scripting environment (ISE), and customize the parameters described in the comments. These are $Template, $ProfileName, $Servers, $DnsSuffix, $DomainName, $TrustedNetwork, and $DNSServers. A full description of each setting is in the comments.
Run the script to generate VPN_Profile.xml and VPN_Profile.ps1 on the desktop.
Listing 1. Understanding MakeProfile.ps1
Cisco Anyconnect Vpn Server
This section explains the example code that you can use to gain an understanding of how to create a VPN Profile, specifically for configuring ProfileXML in the VPNv2 CSP.
After you assemble a script from this example code and run the script, the script generates two files: VPN_Profile.xml and VPN_Profile.ps1. Use VPN_Profile.xml to configure ProfileXML in OMA-DM compliant MDM services, such as Microsoft Intune.
Use the VPN_Profile.ps1 script in Windows PowerShell or Microsoft Endpoint Configuration Manager to configure ProfileXML on the Windows 10 desktop.
Note
To view the full example script, see the section MakeProfile.ps1 Full Script.
Parameters
Configure the following parameters:
$Template. The name of the template from which to retrieve the EAP configuration.
$ProfileName. Unique alphanumeric identifier for the profile. The profile name must not include a forward slash (/). If the profile name has a space or other non-alphanumeric character, it must be properly escaped according to the URL encoding standard.
$Servers. Public or routable IP address or DNS name for the VPN gateway. It can point to the external IP of a gateway or a virtual IP for a server farm. Examples, 208.147.66.130 or vpn.contoso.com.
$DnsSuffix. Specifies one or more commas separated DNS suffixes. The first in the listis also used as the primary connection-specific DNS suffix for the VPN Interface. The entire list will also be added into the SuffixSearchList.
$DomainName. Used to indicate the namespace to which the policy applies. When a Name query is issued, the DNS client compares the name in the query to all of the namespaces under DomainNameInformationList to find a match. This parameter can be one of the following types:
- FQDN - Fully qualified domain name
- Suffix - A domain suffix that will be appended to the shortname query for DNS resolution. To specify a suffix, prepend a period (.) to the DNS suffix.
$DNSServers. List of comma-separated DNS Server IP addresses to use for the namespace.
$TrustedNetwork. Comma-separated string to identify the trusted network. VPN does not connect automatically when the user is on their corporate wireless network where protected resources are directly accessible to the device.
The following are example values for parameters used in the commands below. Ensure that you change these values for your environment.
Prepare and create the profile XML
The following example commands get EAP settings from the template profile:
Create the profile XML
Important
Any other combination of upper or lower case for 'true' in the following tags results in a partial configuration of the VPN profile:
<AlwaysOn>true</AlwaysOn>
<RememberCredentials>true</RememberCredentials>
Output VPN_Profile.xml for Intune
You can use the following example command to save the profile XML file:
Output VPN_Profile.ps1 for the desktop and Configuration Manager
The following example code configures an AlwaysOn IKEv2 VPN Connection by using the ProfileXML node in the VPNv2 CSP.
You can use this script on the Windows 10 desktop or in Configuration Manager.
Define key VPN profile parameters
Escape special characters in the profile
Define WMI-to-CSP Bridge properties
Determine user SID for VPN profile:
Define WMI session:
Detect and delete previous VPN profile:
Create the VPN profile:
Save the profile XML file
MakeProfile.ps1 Full Script
Most examples use the Set-WmiInstance Windows PowerShell cmdlet to insert ProfileXML into a new instance of the MDM_VPNv2_01 WMI class.
However, this does not work in Configuration Manager because you cannot run the package in the end users' context. Therefore, this script uses the Common Information Model to create a WMI session in the user's context, and then it creates a new instance of the MDM_VPNv2_01 WMI class in that session. This WMI class uses the WMI-to-CSP bridge to configure the VPNv2 CSP. Therefore, by adding the class instance, you configure the CSP.
Important
WMI-to-CSP bridge requires local admin rights, by design. To deploy per user VPN profiles you should be using Configuration Manager or MDM.
Note
The script VPN_Profile.ps1 uses the current user's SID to identify the user's context. Because no SID is available in a Remote Desktop session, the script does not work in a Remote Desktop session. Likewise, it does not work in a Hyper-V enhanced session. If you're testing a Remote Access Always On VPN in virtual machines, disable enhanced session on your client VMs before running this script.
The following example script includes all of the code examples from previous sections. Ensure that you change example values to values that are appropriate for your environment.

Configure the VPN client by using Windows PowerShell
To configure the VPNv2 CSP on a Windows 10 client computer, run the VPN_Profile.ps1 Windows PowerShell script that you created in the Create the profile XML section. Open Windows PowerShell as an Administrator; otherwise, you'll receive an error saying, Access denied.
After running VPN_Profile.ps1 to configure the VPN profile, you can verify at any time that it was successful by running the following command in the Windows PowerShell ISE:
Successful results from the Get-WmiObject cmdlet
The ProfileXML configuration must be correct in structure, spelling, configuration, and sometimes letter case. If you see something different in structure to Listing 1, the ProfileXML markup likely contains an error.
If you need to troubleshoot the markup, it is easier to put it in an XML editor than to troubleshoot it in the Windows PowerShell ISE. In either case, start with the simplest version of the profile, and add components back one at a time until the issue occurs again.
Configure the VPN client by using Configuration Manager
Cisco Anyconnect Client Download
In Configuration Manager, you can deploy VPN profiles by using the ProfileXML CSP node, just like you did in Windows PowerShell. Here, you use the VPN_Profile.ps1 Windows PowerShell script that you created in the section Create the ProfileXML configuration files.
To use Configuration Manager to deploy a Remote Access Always On VPN profile to Windows 10 client computers, you must start by creating a group of machines or users to whom you deploy the profile. In this scenario, create a user group to deploy the configuration script.
Create a user group
In the Configuration Manager console, open Assets and ComplianceUser Collections.
On the Home ribbon, in the Create group, click Create User Collection.
On the General page, complete the following steps:
a. In Name, type VPN Users.
b. Click Browse, click All Users and click OK.
c. Click Next.
On the Membership Rules page, complete the following steps:
a. In Membership rules, click Add Rule, and click Direct Rule. In this example, you're adding individual users to the user collection. However, you might use a query rule to add users to this collection dynamically for a larger-scale deployment.
b. On the Welcome page, click Next.
c. On the Search for Resources page, in Value, type the name of the user you want to add. The resource name includes the user's domain. To include results based on a partial match, insert the % character at either end of your search criterion. For example, to find all users containing the string 'lori,' type %lori%. Click Next.
d. On the Select Resources page, select the users you want to add to the group, and click Next.
e. On the Summary page, click Next.
f. On the Completion page, click Close.
Back on the Membership Rules page of the Create User Collection Wizard, click Next.
On the Summary page, click Next.
On the Completion page, click Close.
After you create the user group to receive the VPN profile, you can create a package and program to deploy the Windows PowerShell configuration script that you created in the section Create the ProfileXML configuration files.
Create a package containing the ProfileXML configuration script
Host the script VPN_Profile.ps1 on a network share that the site server computer account can access.
In the Configuration Manager console, open Software LibraryApplication ManagementPackages.
On the Home ribbon, in the Create group, click Create Package to start the Create Package and Program Wizard.
On the Package page, complete the following steps:
a. In Name, type Windows 10 Always On VPN Profile.
b. Select the This package contains source files check box, and click Browse.
c. In the Set Source Folder dialog box, click Browse, select the file share containing VPN_Profile.ps1, and click OK.Make sure you select a network path, not a local path. In other words, the path should be something like fileservervpnscript, not c:vpnscript.
Click Next.
On the Program Type page, click Next.
On the Standard Program page, complete the following steps:
a. In Name, type VPN Profile Script.
b. In Command line, type PowerShell.exe -ExecutionPolicy Bypass -File 'VPN_Profile.ps1'.
c. In Run mode, click Run with administrative rights.
d. Click Next.
On the Requirements page, complete the following steps:
a. Select This program can run only on specified platforms.
b. Select the All Windows 10 (32-bit) and All Windows 10 (64-bit) check boxes.
c. In Estimated disk space, type 1.
d. In Maximum allowed run time (minutes), type 15.
e. Click Next.
On the Summary page, click Next.
On the Completion page, click Close.
With the package and program created, you need to deploy it to the VPN Users group.
Deploy the ProfileXML configuration script
In the Configuration Manager console, open Software LibraryApplication ManagementPackages.
In Packages, click Windows 10 Always On VPN Profile.
On the Programs tab, at the bottom of the details pane, right-click VPN Profile Script, click Properties, and complete the following steps:
a. On the Advanced tab, in When this program is assigned to a computer, click Once for every user who logs on.
b. Click OK.
Right-click VPN Profile Script and click Deploy to start the Deploy Software Wizard.
On the General page, complete the following steps:
a. Beside Collection, click Browse.
b. In the Collection Types list (top left), click User Collections.
c. Click VPN Users, and click OK.
d. Click Next.
On the Content page, complete the following steps:
a. Click Add, and click Distribution Point.
b. In Available distribution points, select the distribution points to which you want to distribute the ProfileXML configuration script, and click OK.
c. Click Next.
On the Deployment settings page, click Next.
On the Scheduling page, complete the following steps:
a. Click New to open the Assignment Schedule dialog box.
b. Click Assign immediately after this event, and click OK.
c. Click Next.
On the User Experience page, complete the following steps:
Select the Software Installation check box.
Click Summary.
On the Summary page, click Next.
On the Completion page, click Close.
With the ProfileXML configuration script deployed, sign in to a Windows 10 client computer with the user account you selected when you built the user collection. Verify the configuration of the VPN client.
Note
The script VPN_Profile.ps1 does not work in a Remote Desktop session. Likewise, it does not work in a Hyper-V enhanced session. If you're testing a Remote Access Always On VPN in virtual machines, disable enhanced session on your client VMs before continuing.
Verify the configuration of the VPN client
In Control Panel, under SystemSecurity, click Configuration Manager.
In the Configuration Manager Properties dialog, on the Actions tab, complete the following steps:
a. Click Machine Policy Retrieval & Evaluation Cycle, click Run Now, and click OK.
b. Click User Policy Retrieval & Evaluation Cycle, click Run Now, and click OK.
c. Click OK.
Close the Control Panel.
You should see the new VPN profile shortly.
Configure the VPN client by using Intune
To use Intune to deploy Windows 10 Remote Access Always On VPN profiles, you can configure the ProfileXML CSP node by using the VPN profile you created in the section Create the ProfileXML configuration files, or you can use the base EAP XML sample provided below.
Note
Intune now uses Azure AD groups. If Azure AD Connect synced the VPN Users group from on-premises to Azure AD, and users are assigned to the VPN Users group, you are ready to proceed.
Create the VPN device configuration policy to configure the Windows 10 client computers for all users added to the group. Since the Intune template provides VPN parameters, only copy the <EapHostConfig> </EapHostConfig> portion of the VPN_ProfileXML file.
Create the Always On VPN configuration policy
Sign into the Azure portal.
Go to Intune > Device Configuration > Profiles.
Click Create Profile to start the Create profile Wizard.
Enter a Name for the VPN profile and (optionally) a description.
Under Platform, select Windows 10 or later, and choose VPN from the Profile type drop-down.
Tip
If you are creating a custom VPN profileXML, see Apply ProfileXML using Intune for the instructions.
Under the Base VPN tab, verify or set the following settings:
Connection name: Enter the name of the VPN connection as it appears on the client computer in the VPN tab under Settings, for example, Contoso AutoVPN.
Servers: Add one or more VPN servers by clicking Add.
Description and IP Address or FQDN: Enter the description and IP Address or FQDN of the VPN server. These values must align with the Subject Name in the VPN server's authentication certificate.
Default server: If this is the default VPN server, set to True. Doing this enables this server as the default server that devices use to establish the connection.
Connection type: Set to IKEv2.
Always On: Set to Enable to connect to the VPN automatically at the sign-in and stay connected until the user manually disconnects.
Remember credentials at each logon: Boolean value (true or false) for caching credentials. If set to true, credentials are cached whenever possible.
Copy the following XML string to a text editor:
Important
Any other combination of upper or lower case for 'true' in the following tags results in a partial configuration of the VPN profile:
<AlwaysOn>true</AlwaysOn>
<RememberCredentials>true</RememberCredentials>Replace the <TrustedRootCA>5a 89 fe cb 5b 49 a7 0b 1a 52 63 b7 35 ee d7 1c c2 68 be 4b</TrustedRootCA> in the sample with the certificate thumbprint of your on-premises root certificate authority in both places.
Important
Do not use the sample thumbprint in the <TrustedRootCA></TrustedRootCA> section below. The TrustedRootCA must be the certificate thumbprint of the on-premises root certificate authority that issued the server-authentication certificate for RRAS and NPS servers. This must not be the cloud root certificate, nor the intermediate issuing CA certificate thumbprint.
Replace the <ServerNames>NPS.contoso.com</ServerNames> in the sample XML with the FQDN of the domain-joined NPS where authentication takes place.
Copy the revised XML string and paste into the EAP Xml box under the Base VPN tab and click OK.An Always On VPN Device Configuration policy using EAP is created in Intune.
Sync the Always On VPN configuration policy with Intune
Cisco Anyconnect Always On Vpn Android
To test the configuration policy, sign in to a Windows 10 client computer as the user you added to the Always On VPN Users group, and then sync with Intune.
On the Start menu, click Settings.
In Settings, click Accounts, and click Access work or school.
Click the MDM profile, and click Info.
Click Sync to force an Intune policy evaluation and retrieval.
Close Settings. After synchronization, you see the VPN profile available on the computer.
Cisco Anyconnect Client Vpn
Next steps
You are done deploying Always On VPN. For other features you can configure, see the table below:
Cached
| If you want to.. | Then see.. |
|---|---|
| Configure Conditional Access for VPN | Step 7. (Optional) Configure conditional access for VPN connectivity using Azure AD: In this step, you can fine-tune how authorized VPN users access your resources using Azure Active Directory (Azure AD) conditional access. With Azure AD conditional access for virtual private network (VPN) connectivity, you can help protect the VPN connections. Conditional Access is a policy-based evaluation engine that lets you create access rules for any Azure Active Directory (Azure AD) connected application. |
| Learn more about the advanced VPN features | Advanced VPN Features: This page provides guidance on how to enable VPN Traffic Filters, how to configure Automatic VPN connections using App-Triggers, and how to configure NPS to only allow VPN Connections from clients using certificates issued by Azure AD. |
